Creating a Network That Uses an Enterprise AAA Server
You can create a network that authenticates users against a remote Authentication, Authorization, and Accounting (AAA) server. Before you begin, note the IP address, port, and shared secret for your primary and (if applicable) secondary RADIUS servers.
In non-proxy mode, an AP sends RADIUS requests directly to a RADIUS server. The outbound connection is from the AP to the IP/FQDN of the RADIUS server on the RADIUS port used by the RADIUS service. If this is a Internet or external RADIUS system, the APs must be able to reach the server from their locations, for example, via NAT or public routing.
In proxy mode, the controller sends outbound RADIUS queries on behalf of the AP for the RADIUS server. In this mode, the cloud controller performs the outbound connection on the required port, and customers do not need to configure firewall rules, since the cloud initiates the request. If you are hosting the RADIUS system, you must allow inbound connectivity to a routable or NATed IP address on the RADIUS port configured in the WLAN. In proxy mode, all RADIUS requests from the AP to the controller pass over the existing control tunnel.
-
In the navigation bar, select
Wi-Fi > Wi-Fi
Networks > Wi-Fi Networks
List.
The Wi-Fi Networks page is displayed.
-
Click Add Wi-Fi
Network. Alternatively, select an Enterprise AAA (802.1X) network
from the network list by clicking the radio button next to the Name column and
then click Clone.
The Create New Network page is displayed.
-
Complete the following settings
on the Network Details page.
- Network Name: Enter a name (2–32 characters) for the network. By default, this name is also used as the SSID.
- (Optional) Set different
SSID: Click Set different
SSID to configure an SSID that differs from the network
name. The SSID field is displayed.
- SSID: Enter an SSID name (2–32 characters; up to 32 bytes for UTF‑8 non‑Latin characters).
- (Optional) Description: Enter a description to help you identify the network.
- Network
Type: Select Enterprise AAA
(802.1X). The structure diagram of an Enterprise AAA (802.1X) network is displayed.Note: If you used the Clone option, the Network Type is already set to Enterprise AAA (802.1X).
-
Click Next.
The AAA Settings page is displayed.
Create New Network - AAA Settings 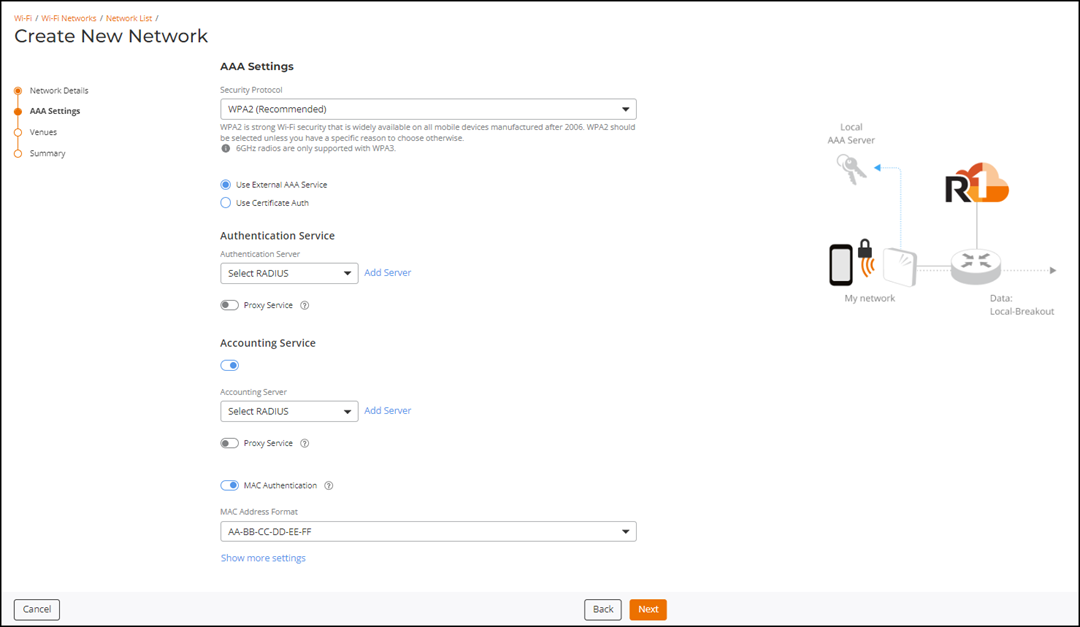
-
Security Protocol: Select the security protocol from the
drop-down list. The options are:
- WPA2 (Recommended) (default)
- WPA3
- WPA2/WPA3 mixed mode
Note: WPA2 provides strong Wi‑Fi security and is supported on all mobile devices manufactured after 2006, making it the recommended choice unless there is a specific need for an alternative. Devices with 6 GHz radios require WPA3, which offers the highest level of Wi‑Fi security but is only supported on devices manufactured after 2019. WPA2/WPA3 mixed mode allows devices to connect using either WPA3 or WPA2, which remains widely compatible. -
Encryption Type:
This field appears only when WPA3 is selected. Choose an encryption type from the drop-down
list:
- AES (default)
- AES-GCMP-256
Create New Network – Encryption Type for WPA3 in the AAA Settings Page 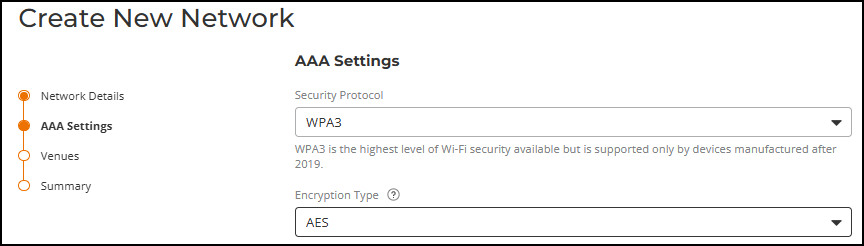 Note: 11ac Wave 1 APs do not support the AES-GCMP-256 encryption type, and therefore cannot operate on SSIDs that use this encryption. For a list of Wi-Fi 11ac Wave 1 indoor and outdoor APs supported by RUCKUS One, refer to https://www.ruckusnetworks.com/ruckus-one-supported-network-devices.Note: When AES-GCMP-256 encryption is selected, the 802.11r Fast BSS Transition option does not appear in the Networking section when you select Show more settings.Note: According to the WPA3 Specification (version 2 or later), AES-GCMP-256 only supports the following cipher suites. Depending on the client type and OS, some clients may refuse to connect to the WLAN if your RADIUS server does not use one of these required cipher suites:
Note: 11ac Wave 1 APs do not support the AES-GCMP-256 encryption type, and therefore cannot operate on SSIDs that use this encryption. For a list of Wi-Fi 11ac Wave 1 indoor and outdoor APs supported by RUCKUS One, refer to https://www.ruckusnetworks.com/ruckus-one-supported-network-devices.Note: When AES-GCMP-256 encryption is selected, the 802.11r Fast BSS Transition option does not appear in the Networking section when you select Show more settings.Note: According to the WPA3 Specification (version 2 or later), AES-GCMP-256 only supports the following cipher suites. Depending on the client type and OS, some clients may refuse to connect to the WLAN if your RADIUS server does not use one of these required cipher suites:- TLS_ECDHE_ECDSA_WITH_AES_256_GCM_SHA384: ECDHE and ECDSA using the 384-bit prime modulus curve P-384.
- TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384: ECDHE using the 384-bit prime modulus curve P-384 and RSA ≥ 3072-bit modulus.
- TLS_DHE_RSA_WITH_AES_256_GCM_SHA384: RSA ≥ 3072-bit modulus and DHE ≥ 3072-bit modulus.
-
Select an authentication method.
By default, Use External AAA Service is selected.
- Use External AAA Service: Configure the required authentication, accounting, and identity settings using an external AAA server.
- Use Certificate Auth: Authenticate users using a certificate authority. Select up to five certificate templates from the Certificate Template drop‑down list. If the required template is not available, click Add to create a new certificate template. Refer to Adding a Certificate Template for instructions on how to add a certificate template.
-
Authentication
Service: Toggle the switch on to enable this option and select
the existing RADIUS Server from the Authentication
Server drop-down list.
If the server is not available, you can create a new one; click Add Server, complete the fields in the Add AAA server sidebar, and click Add. Then select the newly created RADIUS from the drop‑down list. Refer to Adding and Managing a RADIUS Server.Note: If both an Authentication Service RADIUS server and Access Control profiles (enabled in Show More Settings > Network Control) are set for the same network, then the access controls configured for the Authentication Service (through User Roles mapped to the RADIUS server) take precedence.Note: This field appears only when Use External AAA Service is selected.
- Proxy
Service: Toggle the switch on to enable the proxy
service.Note: The controller acts as a proxy in 802.1X networks. When access points send authentication and accounting messages to the controller, the controller forwards these messages to an external AAA server.Note: The Proxy Service must be enabled to display the MAC Registration List and External MAC Auth options.
- Proxy
Service: Toggle the switch on to enable the proxy
service.
-
Accounting
Service: Toggle the switch on to enable this option and select
the existing RADIUS Server from the Accounting Server
drop-down list.
If the server is not available, you can create a new one; click Add Server, complete the fields in the Add AAA server sidebar, and click Add. Then select the newly created RADIUS from the drop‑down list. Refer to Adding and Managing a RADIUS Server.
- Proxy
Service: Toggle the switch on to enable the proxy
service.Note: Use the controller as a proxy in 802.1X networks. When access points send authentication and accounting messages to the controller, the controller forwards these messages to an external AAA server.
- Proxy
Service: Toggle the switch on to enable the proxy
service.
-
Identity Group:
Select an identity group from the drop‑down list.
If the identity group is not yet defined, you can create a new one; click Add, complete the fields in the Create Identity Group sidebar, and click Apply. You can then select the newly created identity group from the Identity Group drop-down list. Refer to Adding an Identity Group for information on how to create a new identity group.
You can click View Details to view the identity group details in the Identity Group sidebar.
Note:- When you select an identity group, all devices that join the network automatically become identities within that group, as shown on the Identity Group page. Users can select an existing identity group or create a new one.
- During network editing, you cannot remove the originally selected identity group; however, you can change it to a different identity group. The identity configuration section does not apply to the MAC Registration List when MAC Authentication is enabled.
- This field appears only when Use External AAA Service is selected.
-
MAC
Authentication: Toggle the MAC
Authentication switch on to add an additional security layer to
the network. When enabled, the system displays the MAC Registration
List and External MAC Auth
options. The MAC Registration List does not support MAC address format
selection. MAC Authentication is disabled by default.
Note:
-
MAC Authentication enhances security for corporate networks by sending client MAC addresses to the configured RADIUS servers for authentication and accounting. Changing the MAC Authentication setting requires creating new MAC authentication settings; the system does not support editing existing settings.
-
When MAC Authentication is enabled using either a MAC Registration List or External MAC Auth, the system enables Dynamic VLAN automatically. Access the Dynamic VLAN option by clicking Show more settings and selecting the VLAN sub‑tab.
-
When you configure a MAC Registration List, also create a new Identity profile and associate it with a client device. Refer to Adding an Identity and Adding a Device to an Identity for more information.
-
-
MAC Registration
List: Select MAC Registration
List by clicking the corresponding radio button.
The Select MAC Registration List drop‑down list is displayed. Select an existing MAC registration list or click Add to create a new one. When you click Add, the Add MAC Registration List dialog box is displayed.
Add MAC Registration List 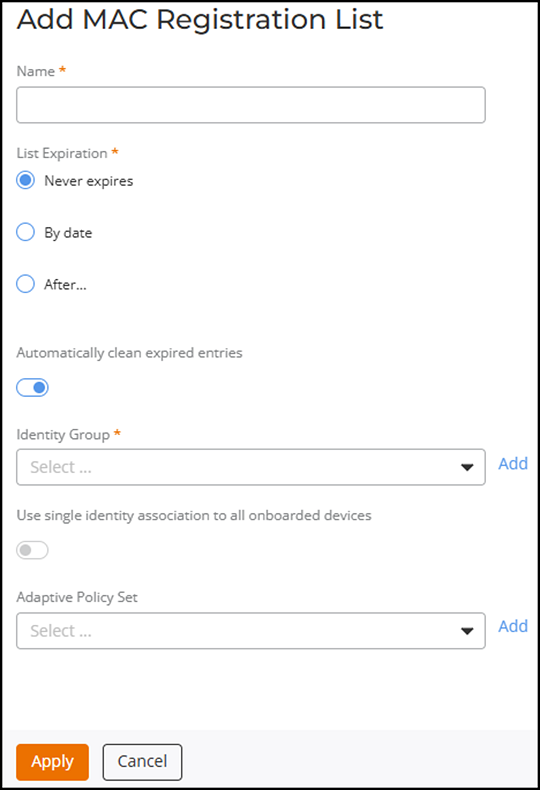 Note: If MAC registration is enabled, RUCKUS One processes the initial authentication request using the MAC registration list. However, if the MAC registration list is not selected, the request is forwarded to the AAA server.Complete the following to add a new MAC Registration List:
Note: If MAC registration is enabled, RUCKUS One processes the initial authentication request using the MAC registration list. However, if the MAC registration list is not selected, the request is forwarded to the AAA server.Complete the following to add a new MAC Registration List:- Name: Enter a name for the MAC Registration List.
- List Expiration: Select an expiration option for the list. Options include Never Expires, By Date (provide an expiration date for the list), or After (provide a duration in hours, days, weeks, months, or years).
- Automatically clean expired entries: Toggle the Automatically clean expired entries switch on to clean expired entries in the list.
- Identity Group: Select an identity group from the drop-down list or click Add to add one. You can also enable Use single identity association to all onboarded devices to assign the same identity to all devices.
- Adaptive Policy Set: Select a policy set from the drop-down list or click Add to add one.
Note: You can associate only one MAC Registration List with each SSID. Adaptive policy sets configured with the MAC Registration List do not apply because external AAA authentication occurs after the policy evaluation stage. -
External MAC
Auth: Select External MAC Auth
by clicking the corresponding radio button.
The MAC Address Format drop-down list is displayed.
- MAC Address
Format: Select the MAC Address
Format from the drop-down list to enable external MAC
authentication. Supported MAC address formats include the following:
- Upper case MAC address separated by colons: 70:EA:5A:78:A1:A0
- Upper case MAC address separated by hyphens: 70-EA-5A-78-A1-A0
- Upper case MAC in a continuous string: 70EA5A78A1A0
- Lower case MAC address separated by colons: 70:ea:5a:78:a1:a0
- Lower case MAC address separated by hyphens: 70-ea-5a-78-a1-a0
- Lower case MAC in a continuous string: 70ea5a78a1a0
- MAC Address
Format: Select the MAC Address
Format from the drop-down list to enable external MAC
authentication. Supported MAC address formats include the following:
-
Click Show more
settings.
By default, the VLAN sub-tab is displayed. Each sub-tab includes additional Wi-Fi configuration options. Refer to Configuring Additional Settings for a Wi-Fi Network to configure each of the available settings.
Note:Demonstration of Advanced Settings for a Wi-Fi Network. This video explains advanced settings for a Wi-Fi network and walks you through the process of configuring them.
-
Click Next.
The Venues page is displayed.
-
Select one or more venues to activate
the network by clicking the checkbox alongside the venue name, and then toggle the switch
on in the Activated
column.
The details in the APs, Radios, and Scheduling columns are displayed for all the activated venues. By default, this network configuration applies across All APs and their applicable radio bands and is scheduled to be available 24/7.Note: The Scheduling column displays availability based on the local time zone of the venue’s AP devices (for example, UTC offsets).
-
Click the All APs hyperlink in the
APs column or the list of
radios in the Radios column to
configure APs and radio-frequency bands for the selected venue.
The Select APs dialog box is displayed. Select one of the following options:
- All APs: Select
All APs to
activate the network on all current and future APs for this venue. Choose a radio
band from the drop-down list. You can choose one or more of the supported radio
bands.
Select APs 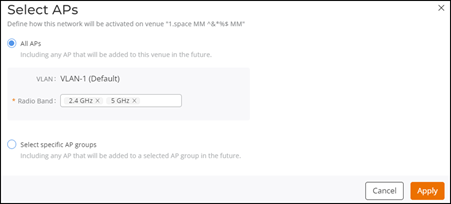
- Select specific AP
groups: Select Select specific AP
groups to activate the network on specific AP groups, including any
AP added to the selected AP groups in the future. The APs not assigned to any
group option is displayed with a checkbox and a reminder to select
an AP Group.
Click the APs not assigned to any group checkbox; the VLAN and Radio Band options are displayed:
Select Specific AP Groups 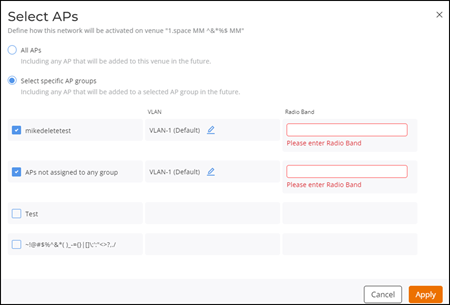
- VLAN: Select
VLAN-1,
which is selected by default. Click the
 icon,
and select a VLAN or a pool from the drop-down list. Depending on the selection, enter the
VLAN ID or select a pool from the drop-down list.
icon,
and select a VLAN or a pool from the drop-down list. Depending on the selection, enter the
VLAN ID or select a pool from the drop-down list. - Radio Band: Select one or more supported radio bands from the drop-down list for the selected AP group.
- Click Apply.
- All APs: Select
All APs to
activate the network on all current and future APs for this venue. Choose a radio
band from the drop-down list. You can choose one or more of the supported radio
bands.
-
Click the 24/7 hyperlink in the
Scheduling
column to customize the schedule.
The Schedule for Network <network-name> in Venue <venue-name> dialog box is displayed.
Schedule for Network Dialog Box  You can choose 24/7 or Custom Schedule. Configure the following if you select Custom Schedule:
You can choose 24/7 or Custom Schedule. Configure the following if you select Custom Schedule:- Click Custom Schedule to
customize the network schedule as required.The Custom Schedule has Basic and Advanced tabs.Note: The venue time zone appears at the bottom of the dialog box.
- On the Basic tab, you can
configure the following:
Schedule for Network - Basic Configuration 
- Start Date:
Displays the date when the schedule begins. You can select any future date
using the date picker. The schedule always uses the local time of the AP
devices.Note: When the Start Date is today, time slots that have already passed are disabled.
- (Optional) All day: Select this option to make the network available for the entire day. When All day is selected, the From and To fields automatically disappear.
- From and
To:
These fields appear only when All day is not
selected. You can select the start and end times in 15‑minute intervals, where
the From
time ranges from 00:00 to 23:45, the To time ranges
from 00:15 to 24:00, and the To time must
always be later than the From time.Note: The selected times follow the local time of the venue’s AP devices.
- Select a repeat rule to
determine how the network availability repeats after the Start Date. The
available options are Do not repeat
(default), Repeat
Daily, Repeat Weekly, and Repeat Monthly.
Note: The Do not repeat option displays a one‑time schedule for the selected Start Date.
- End Date:
- Select None or Select date if Repeat Daily is selected. Pick an end date from the date picker when Select date is chosen.
- Select the required weekday, and then select None or Select date if Repeat Weekly is selected. Pick an end date from the date picker when Select date is chosen.
- Select a monthly
recurrence option such as Day <date> of every month, the <nth>
<weekday> of every month, or the last <weekday> of every
month, and then select None or
Select
date if Repeat
Monthly is selected. Pick an end date from the date picker
when Select
date is chosen.Note: Selecting at least one weekday is mandatory if Repeat Weekly is selected, and selecting a monthly recurrence option is mandatory if Repeat Monthly is selected.Note: Monthly options depend on whether the Start Date falls on the first through fourth weekday occurrence or the last weekday of the month. Daily, Weekly, and Monthly repeat rules deactivate the network automatically at midnight on the selected End Date.Note: If an End Date is selected, the schedule ends at midnight on that date.
- Start Date:
Displays the date when the schedule begins. You can select any future date
using the date picker. The schedule always uses the local time of the AP
devices.
- On the Advanced tab, you can
configure the following:
Schedule for Network - Advanced Configuration 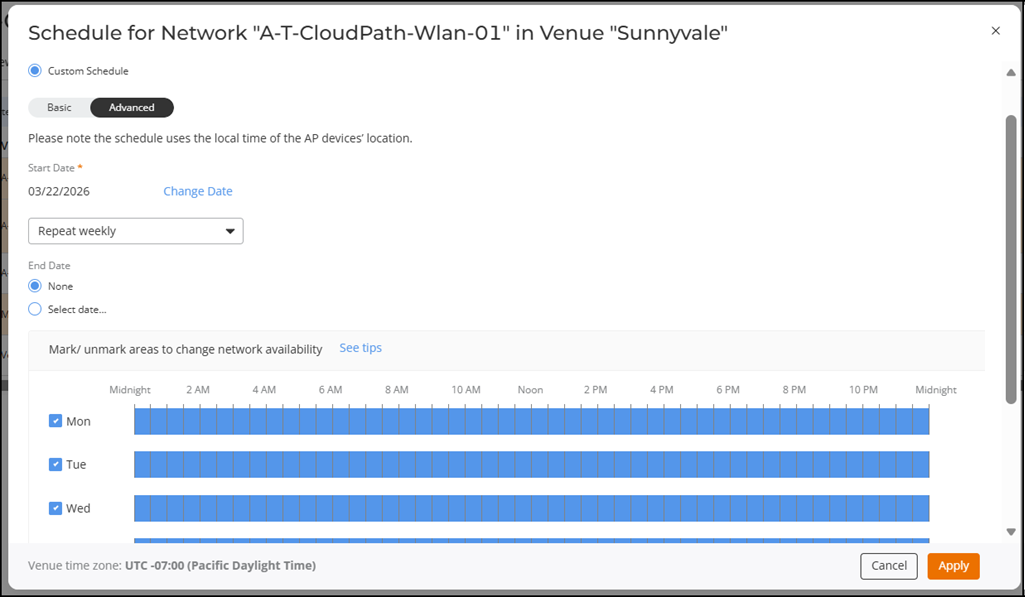
- Start Date:
Displays the date when the schedule begins. You can select any future date
using the date picker. The schedule always uses the local time of the AP
devices.Note: When the Start Date is today, time slots that have already passed are disabled.
- (Optional) Select a repeat
rule to determine how the network availability repeats after the Start Date.
The available options are Do not repeat
(default) and Repeat
Weekly. Note: The Do not repeat option displays a one‑time weekly schedule for the selected Start Date. The network automatically deactivates at the end of the last active time slot.
- End Date:
- Select None or
Select
date if Repeat Weekly
is selected. Pick an end date from the date picker when Select date is
chosen.Note: When the Start date is chosen, selecting a date from the date picker is mandatory.Note: If an End Date is selected, the schedule ends at midnight on that date.
- Select None or
Select
date if Repeat Weekly
is selected. Pick an end date from the date picker when Select date is
chosen.
- Mark the required time on the weekly grid to enable or disable network availability in fifteen‑minute intervals. You can click a single slot or click and drag to update multiple adjacent slots. A full day can be enabled or disabled using the checkbox next to each day. Dragging across a range of slots changes all slots to the opposite state of the first slot selected.
- Click See tips to view guidance on how to activate or deactivate the network for the entire day, individual time slots, or multiple adjacent time slots. The See tips option opens the Network Scheduler Tips window, which explains how to use the checkbox for full‑day selection, how to click individual slots, and how to drag across the timeline to update multiple time slots.
- Start Date:
Displays the date when the schedule begins. You can select any future date
using the date picker. The schedule always uses the local time of the AP
devices.
- Click Apply. The hyperlink
updates to ON
now. When you hover over it, it displays the time until which the
scheduler will remain active (<Day> <Time>).Note: If no weekday is selected, the message Network is configured to be unavailable at all times is displayed on the Network Scheduling dialog box. You can continue by clicking OK or by clicking Cancel to configure the required days.
Schedule for Network - Advanced Configuration 
- Click Custom Schedule to
customize the network schedule as required.
-
Toggle the Network Tunneling switch on to
define how network traffic is tunneled at the venue. When toggled on, a Tunnel: <venue-name>
sidebar is displayed.
Note: The Network Tunneling switch is displayed only when the venue is Activated.
- Select a Tunneling Method from the drop-down.
- If you choose SoftGRE, select a
SoftGRE
profile and optionally enable and configure IPsec. (Refer to
Creating a SoftGRE Profile and Adding an SD-LAN Service).
The SD-LAN option is available only when RUCKUS Edge devices are present.
- Click Add to save and apply.
-
Click the All APs hyperlink in the
APs column or the list of
radios in the Radios column to
configure APs and radio-frequency bands for the selected venue.
-
Click Next.
The Summary page is displayed.
-
Click Finish.
Network Summary 